eXcelkey Product descriptions (Based on Decentralized & Blockchain)
Current Status of 2FA Products
Current Status of 2FA Products - "Electronic Signature, 2nd Certification Market Rapid Growth"
| Carrier certification | OTP (S/W, H/W) | Electronic signature/Insurance company | SMS OTP | Enterprise 2nd certification | |
|---|---|---|---|---|---|
| Product type | carrier principal identification App | Google OTP, bank OTP terminal, etc. | Self-certification + electronic signature | Authentication by SMS OTP number | Program Secondary Certification, I/O Control |
| Internet service principal authentication / Payment Authorization | Virtual currency exchange, bank internet banking | Self-certification, Electronic signature, Insurance Architect, insurance accident victim, Hospitals and patients, Health care | Transferring various Internet services, Remittance, Cryptographic Money Exchange and Asset Platform, Online/Mobile Game Service | ERP, Intranet, accounting/accounting program, Corporate Internal Programs, In/Out Control, Research Institute | |
| Public & Private |
Public | Public | Public & Private | Public & Private | Private |
eXcelKey Key use points
ERP
Insurance company
Corporate intranet
Online Payment/Financial Platform
PC/Mobile Games
Legal/Accounting management
University/Public office
R&D Research Institute/R&D
Hospital/Healthcare center
Cryptocurrency exchange
eXcelKey Service introduction

- No touch, no click, no input thanks to FIDO biometric verification technology
- It is not necessary to remember and input password or OTP authentication number
- eXcelKey Application enables authentication of all types and only requires an easy installation & registration process
- Simply use one-time QR code scan, when registering for a new verification
- Application of separated data system without the existence of any original data
- Blockchain prevents data sabotage through matching hash value principle
- Multi-security through self-certification with support of FIDO
- More secure by allowing only your device, user IP & packets
- Strong secondary authentication protects your data, even if ID & PW is leaked

- 50% to 80% cheaper than credit card companies, SMS OTP, and ARS 2CH certification
- Eliminate development and server deployment costs (ASP)
- Supports all types of secondary certification (self-identification) and supporys scalability
- Free for 3 months, no immediate commitment

- Large-sized enterprise can provide integrated authentication services to their customers via integrated SSOs
- Customizable development with independent branding
- All types of secondary authentication can be used with an eXcelKey app
- Replace payments, security certification, primary certification and simple authentications
eXcelKey Comparison
excelKEY vs Other
| eXcelkey secondary authentication | Text message | Base | Google OTP | OTP Machine | Certificate | PIN | ID & PW | ||
|---|---|---|---|---|---|---|---|---|---|
| Authentication for devices bound to users | O | O | O | O | O | X | O | X | X |
| User self-confirmation | O | X | X | X | X | X | X | X | X |
| Biometric authentication (FIDO) | O | X | X | X | X | X | X | X | X |
| Authentication related to specific user devices | O | X | X | X | X | X | X | X | X |
| Easy, fast "NO typing" access | O | X | X | X | X | X | X | X | X |
| Prevent Brute force attacks | O | O | O | X | O | O | X | X | X |
| For technical use of blockchain (anti-fabrication) | O | X | X | X | X | X | X | X | X |
| Isolation/Distributed data | O | X | X | X | X | X | X | X | X |
excelKEY vs Google OTP
| Category | Google OTP | eXelkey 2nd authentication | eXelkey 2nd authentication differentiation | |
|---|---|---|---|---|
| Security | To create an authentication code | Created by OTP module (Time based) | Request User-Based (Optional) Direct Generation | Create real-time on authentication request |
| Save Source Data | Save Source | No Source | Maximize security by storing personal information and credentials in distributed nodes and block chains. | |
| Store source data for comparison on server | Blockchain, separation distribution on distributed nodes | |||
| authentication method | 6-8 digits random number | Pin code, pattern, Bio (biodiversity information) | Various means of authentication are provided | |
| Prevention of Assumption | X | O | Authentication using FIDO to compensate for vulnerability to speculative attacks | |
| Generate code with 6-8 digits | Support for authentication using biometric information, numbers, and characters | |||
| Non-Repudiation | X | O | Digital signature method using user's key | |
| S/W Independence | open source base | BaaSid Self-Development and Development of FIDO-related security modules | Complement attack vulnerability to open source | |
| Server transaction | Compare the code entered by the client with the code generated by the server | Receive only authentication results in separate authentication sessions | Identifying devices that pass through their IPs and packets only | |
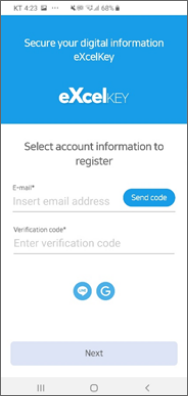
| Convenience/Expandability | Account | Google Account Registration | Register simple account through all mail and SNS | All types of primary and secondary authentication are available |
| Register user | User registers in multiple steps | Easy registration with QR code scan | Provides ease of registration for users | |
| User Identification | X | O | Identifying users based on their own authentication | |
| Extensibility | X | O | 2nd Certification App Operates Exclusive |
Introduction to eXcelKey service details
- ① Device unique value + FIDO + BaaSid Key → Authentication of your device
- ② Subscribe with your Google, Line account etc. in only one second (all SNS and message will be linked in the future)
- ③ Even if Google, Line, and other linked SNS accounts are leaked, they will only work on your dedicated device
- ④ Strong terminal-oriented authentication that identifies only your device IP and normal packets
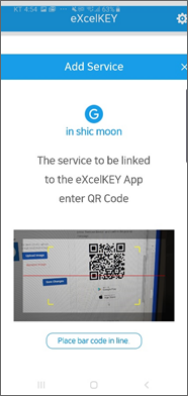
- ① Create one-time QR code and scan to complete new registration in one second
- ② In case of loss of phone, re-register with composite authentication (E-mail + SMS, E-mail + Personal Information Input)
- ③ Various authentication methods such as FIDO, biometric authentication, pin number and pattern are available.
- ④ Authentication without the hassle of remembering and entering a separate OTP number
